🧠 Concept 18: Security (RBAC + Service Accounts + Production 🔐)


🚀 1. Core Idea (1-line)
👉 Kubernetes security controls who can do what using RBAC + Service Accounts
🧠 2. Why Security is Needed (VERY IMPORTANT ⚠️)
Without RBAC:
-
Anyone can delete pods ❌
-
Anyone can access secrets ❌
-
Cluster = unsafe 💀
🔐 3. Authentication vs Authorization (MUST KNOW 🔥)
🔑 Authentication → “Who are you?”
- User / Service Account
🛡️ Authorization → “What can you do?”
- RBAC decides this
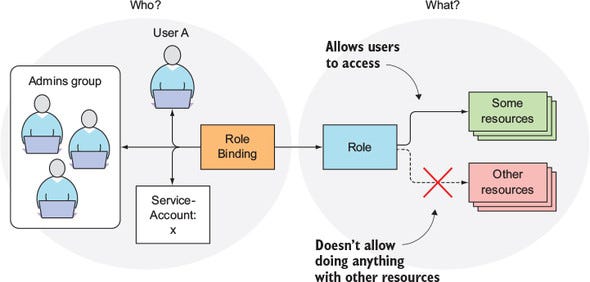
⚙️ 4. RBAC (Role-Based Access Control)
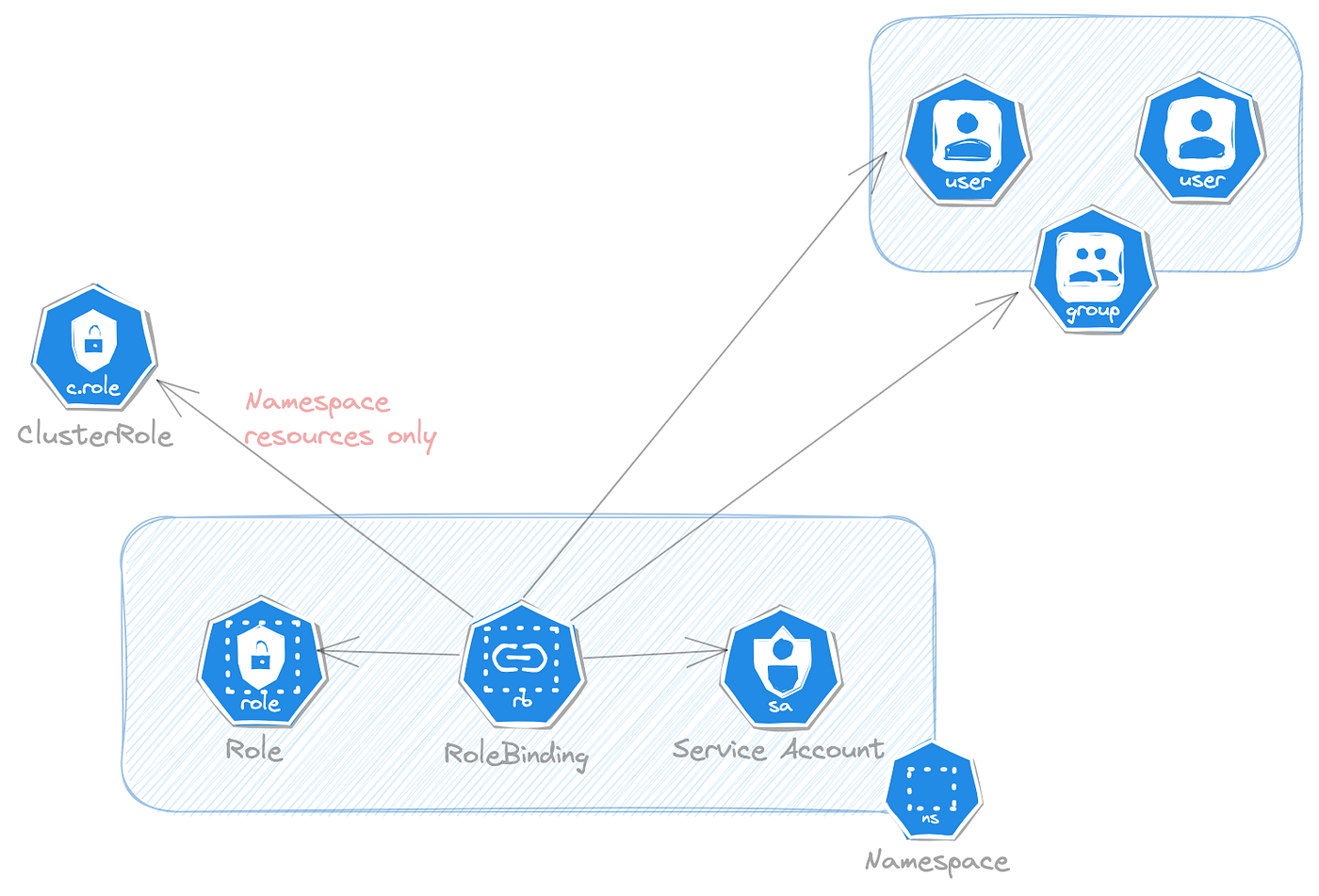
🟢 1. Role
👉 Defines permissions inside a namespace
kind: Role
rules:
- apiGroups: [""]
resources: ["pods"]
verbs: ["get", "list"]🔵 2. RoleBinding
👉 Assigns role to user/service account
kind: RoleBinding
subjects:
- kind: User
name: yash🌐 3. ClusterRole
👉 Same as Role but cluster-wide
🔗 4. ClusterRoleBinding
👉 Binds ClusterRole globally
🔥 5. Flow (VERY IMPORTANT 🔥)
User → API Server → RBAC check → Allowed / Denied🧠 6. Service Accounts (VERY IMPORTANT 🔥)
👉 Used by pods to talk to Kubernetes API
Example:
apiVersion: v1
kind: ServiceAccount
metadata:
name: my-sa👉 Attach to pod:
spec:
serviceAccountName: my-sa💥 7. Real-world Example
Pod wants to:
-
Read secrets
-
Access API
👉 Needs:
-
Service Account
-
Proper Role
⚠️ 8. VERY IMPORTANT Security Rules
-
Never give
cluster-admin❌ -
Follow least privilege principle
-
Rotate secrets
🔒 9. Secrets Security (Advanced)
Earlier we saw Secrets 👀
👉 For production:
-
Enable encryption at rest
-
Use:
-
AWS Secrets Manager
-
HashiCorp Vault
🔥 10. Real DevOps Insight
In companies:
-
Dev → limited access
-
CI/CD → controlled access
-
Apps → service accounts
👉 Everything controlled via RBAC
⚠️ 11. Common Mistakes
❌ Giving full access
❌ Not using service accounts
❌ Hardcoding credentials
💼 12. Interview Answer
👉 “Kubernetes security is implemented using RBAC for authorization and Service Accounts for pod-level identity, ensuring controlled and secure access to cluster resources.”
⚡ 13. CKA Commands
kubectl get roles
kubectl get rolebindings
kubectl get serviceaccounts🧠 14. Memory Trick
👉 RBAC = permissions 🎫
👉 Service Account = identity 🆔
🔥 15. Pro Insight (Real-world)
👉 Combine:
-
RBAC
-
Network Policies
-
Pod Security
👉 For full cluster security 🔐
🚀 Next Step
Bol:
👉 “next”
Then we go to FINAL:
🔥 Concept 19: Troubleshooting (Debugging K8s like a PRO 💯 — MOST IMPORTANT FOR CKA 🔥)